Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
Account data review for the identifiers 8285431493, mez68436136, 9173980781, 7804091305, and IP 111.90.150.204l requires a disciplined, cross-platform approach. The process maps identifiers, verifies provenance, and enforces governance with minimal exposure. It supports anomaly detection and risk-based monitoring while aligning with policy and ownership rights. The discussion will address practical steps and governance controls that enable timely remediation, but a critical point remains unresolved until key ownership and provenance are confirmed.
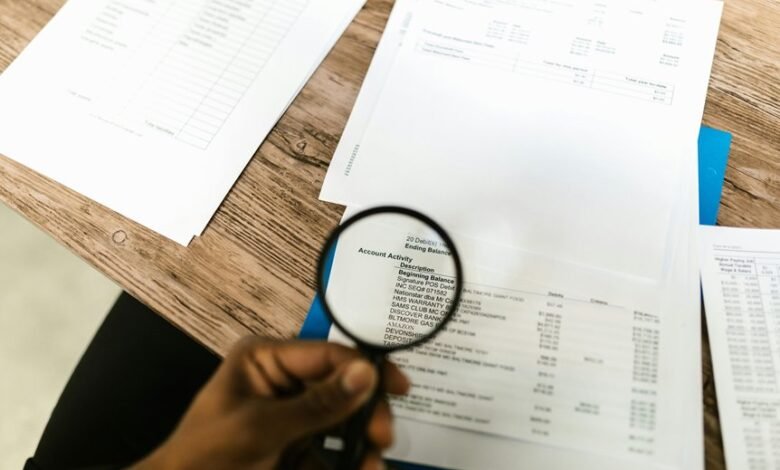
What Is Account Data Review and Why It Matters
Account data review is a systematic process of examining financial and operational data to ensure accuracy, completeness, and compliance.
The practice clarifies data ownership and controls, supporting informed decision making.
It emphasizes data privacy and risk assessment, identifying gaps and mitigation opportunities.
Through standardized checks, organizations align records with policies, protect stakeholders, and sustain trust while enabling lawful, transparent operations.
How to Map Identifiers Across Platforms for Safety
How can identifiers be mapped across platforms to enhance safety while preserving privacy and governance? Cross platform mapping enables unified visibility while segmenting data provenance, reducing privacy gaps.
A structured approach aligns identifiers without exposing raw attributes, supporting anomaly tracking and accountability. This method emphasizes governance, consent, and minimal data sharing to sustain safety without compromising user autonomy.
Practical Steps to Detect Anomalies in Multi-Identifier Data
Effective anomaly detection in multi-identifier data requires a structured, privacy-preserving approach that prioritizes governance and minimal data exposure. The process emphasizes data integrity through disciplined cross referencing and robust account linkage, enabling consistent records. Anomaly scoring methods quantify deviations, supporting objective decision making. Technical controls ensure reproducibility, auditability, and minimal data exposure while preserving user-centric freedom and operational efficiency.
Best Practices for Governance, Compliance, and Ongoing Monitoring
Best Practices for Governance, Compliance, and Ongoing Monitoring require a structured, risk-based framework that aligns policy, process, and technical controls. The approach emphasizes data governance, continuous risk assessment, and transparent platform mapping. It supports proactive anomaly detection, auditing, and controls validation, enabling freedom to innovate while maintaining compliance, accountability, and resilience through disciplined monitoring and timely remediation.
Frequently Asked Questions
Who Is Responsible for Data Accuracy Across Platforms?
Data governance assigns responsibility for accuracy across platforms, with cross platform ownership ensuring consistency and accountability. The framework clarifies roles, drives standardization, and promotes reliable data across environments while preserving freedom to innovate and adapt.
How Often Should Data Mappings Be Reviewed?
Data governance dictates quarterly reviews of data mappings, with ongoing alerts for drift; this sustains data lineage clarity, compliance, and trust. The cadence aligns governance standards, ensuring accuracy while empowering teams with measured, freedom-minded accountability.
What Tools Verify Cross-Platform Identity Consistency?
Tools verification for cross platform identity consistency is achieved via identity governance suites, federated authentication probes, and continuous root-cause analytics; these tools verify cross platform coherence and detect drift across heterogeneous environments with concise reporting.
Can Users Opt Out of Data Collection?
Yes; users may opt out of data collection where offered. The system employs opt out mechanics and data minimization principles, ensuring user consent is respected, with transparent controls and frictionless disengagement for privacy-conscious individuals seeking freedom.
What Are Common False Positives in Anomaly Detection?
Anomaly detection commonly yields false positives due to excessive sensitivity, exaggerating signals into alarm: Common falsehoods arise from misconfigured thresholds, data drift, and noisy baselines, where anomaly noise masquerades as genuine events, prompting unwarranted responses.
Conclusion
In essence, Account Data Review is a vigilant lighthouse guiding cross-platform assets toward safe harbors. By mapping identifiers with disciplined care, it trims ambiguity and illuminates deviations before they escalate. The process stitches governance, provenance, and anomaly scoring into a single, disciplined seam, ensuring compliance and accountability. Like a steady compass in a storm, it enables timely remediation, preserves stakeholder trust, and keeps the data shoreline orderly, transparent, and ready for audit-ready voyage.




